Traditionally OpenSSH has used the OpenSSL-compatible formats PKCS#1 (for RSA)and SEC1 (for EC) for Private keys.
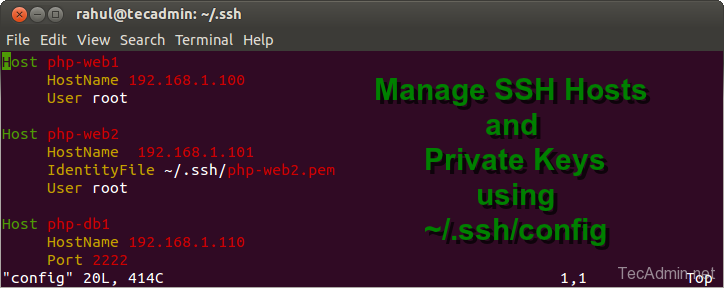
Note that if the SSH private key isn't stored in the file or in the path that the ssh utility expects (for example, the ssh utility might expect the private key to be stored in /.ssh/idrsa), you must explicitly specify the private key filename and location in one of two ways. For example, all my personal projects that need to my personal SSH key with Gitlab are under /Documents/Projects/personal so when the shell hook runs pwd and finds that the current directory is under that path, it automatically sets the GITSSHCOMMAND variables as needed. You need your SSH public key and you will need your ssh private key. Keys can be generated with ssh-keygen. The private key must be kept on Server 1 and the public key must be stored on Server 2. This is completly described in the manpage of openssh, so I will quote a. For more background and examples, see Detailed steps to create SSH key pairs. For additional ways to generate and use SSH keys on a Windows computer, see How to use SSH keys with Windows on Azure. Supported SSH key formats. Azure currently supports SSH protocol 2 (SSH-2) RSA public-private key pairs with a minimum length of 2048 bits.
This week I discovered that it now has its own format too,which is the default output format for some installations of ssh-keygen.
After peeking at the binary I found, much to my dismay - and very much unlikethe ssh public key format (RFC 4253) - that OpenSSH private key format isnot intuitively obvious, I headed to les googles.
The following example will display the public key for the default /root/.ssh/idrsa private key. # ssh-keygen -y Enter file in which the key is (/root/.ssh/idrsa): ssh-rsa AAAAB3NzaC1yc2EAAAABIwAAAQEA5kSivOqhs0U9ZMN20nxFe27QZ3t0lT2zbH7OSX You can also specify the priviate key using -f option.
I searched high and low (or at least past page 2, which is a distinguished markof true dedication), but found no useful information to assauge my curiosity(and habit).
In lieu of the docs I turned to the source. With a combination of theconcentrated efforts of my best code sluething and reverse engineering skills,I believe I have (here below) produced the most complete documentation theInternet has to offer on the subject.
So, without further ado...
OpenSSH Private Keys
On the outside it's PEM encoded. It looks like this:
But, unlike most PEMs, there's no DER inside.
Instead it's the 'proprietary' OpenSSH format, which looks like this:
As you can see (maybe) there's
- A format ID prefix
- Encryption headers
- An unused number for number of keys in the block
- An rfc4253-style ssh public key
- An private key somewhat modeled after the rfc4253 style
- A comment
- Padding for aligning private key to the blocksize
Note that the blocksize is 8 (for unencrypted keys, at least).
The RFC 4253 SSH Public Key format,is used for both the embedded public key and embedded private key key,with the caveat that the private key has a header and footer that must be sliced:
- RSA private keys swap
eandnfornande. - 8 bytes of unused checksum bytes as a header
- n bytes (between 0 and 7) of padding
- bytes > 0x00 and < 0x08 must be trimmed (from the right)
- the padding must be a (right-trimmed) substring of
0x01020304050607 - (that includes the empty substring)
- if the last byte isn't padding, it's part of the comment (0x21 to 0x7e)
Reference Material
The canonical source codeis only available via tarball (.tar.gz).
However, there's also a well-maintained fork (Portable OpenSSH)which has perfectly linkable source code and among them I foundthis to be the file of greatest interest:
Even more particularly, these were the most interesting functions:
sshkey_parse_private2sshkey_private_deserializesshkey_private_serialize_opt
I don't quite remember where, but another piece of information Idiscovered is that when the key isn't encrypted (cipher and kdfvalues are 'none' and 'none') the blocksize is 8 bytes and thevalue of CLFLAG_NONE is also 8:
By AJ ONeal
Did I make your day?
Connect Ssh With Key
(you can learn about the bigger picture I'm working towards on my patreon page )
Please enable JavaScript to view the comments powered by Disqus.-->With a secure shell (SSH) key pair, you can create virtual machines (VMs) in Azure that use SSH keys for authentication. This article shows you how to quickly generate and use an SSH public-private key file pair for Linux VMs. You can complete these steps with the Azure Cloud Shell, a macOS or Linux host.
Note
VMs created using SSH keys are by default configured with passwords disabled, which greatly increases the difficulty of brute-force guessing attacks.
For more background and examples, see Detailed steps to create SSH key pairs.
For additional ways to generate and use SSH keys on a Windows computer, see How to use SSH keys with Windows on Azure.
Supported SSH key formats
Azure currently supports SSH protocol 2 (SSH-2) RSA public-private key pairs with a minimum length of 2048 bits. Other key formats such as ED25519 and ECDSA are not supported.
Create an SSH key pair
Use the ssh-keygen command to generate SSH public and private key files. By default, these files are created in the ~/.ssh directory. You can specify a different location, and an optional password (passphrase) to access the private key file. If an SSH key pair with the same name exists in the given location, those files are overwritten.
The following command creates an SSH key pair using RSA encryption and a bit length of 4096:
If you use the Azure CLI to create your VM with the az vm create command, you can optionally generate SSH public and private key files using the --generate-ssh-keys option. The key files are stored in the ~/.ssh directory unless specified otherwise with the --ssh-dest-key-path option. If an ssh key pair already exists and the --generate-ssh-keys option is used, a new key pair will not be generated but instead the existing key pair will be used. In the following command, replace VMname and RGname with your own values:
Provide an SSH public key when deploying a VM
To create a Linux VM that uses SSH keys for authentication, specify your SSH public key when creating the VM using the Azure portal, Azure CLI, Azure Resource Manager templates, or other methods:
If you're not familiar with the format of an SSH public key, you can display your public key with the following cat command, replacing ~/.ssh/id_rsa.pub with the path and filename of your own public key file if needed:
A typical public key value looks like this example:
If you copy and paste the contents of the public key file to use in the Azure portal or a Resource Manager template, make sure you don't copy any trailing whitespace. To copy a public key in macOS, you can pipe the public key file to pbcopy. Similarly in Linux, you can pipe the public key file to programs such as xclip.
The public key that you place on your Linux VM in Azure is by default stored in ~/.ssh/id_rsa.pub, unless you specified a different location when you created the key pair. To use the Azure CLI 2.0 to create your VM with an existing public key, specify the value and optionally the location of this public key using the az vm create command with the --ssh-key-values option. In the following command, replace myVM, myResourceGroup, UbuntuLTS, azureuser, and mysshkey.pub with your own values:
If you want to use multiple SSH keys with your VM, you can enter them in a space-separated list, like this --ssh-key-values sshkey-desktop.pub sshkey-laptop.pub.
Renci Ssh Private Key Example
SSH into your VM
With the public key deployed on your Azure VM, and the private key on your local system, SSH into your VM using the IP address or DNS name of your VM. In the following command, replace azureuser and myvm.westus.cloudapp.azure.com with the administrator user name and the fully qualified domain name (or IP address):
If you specified a passphrase when you created your key pair, enter that passphrase when prompted during the login process. The VM is added to your ~/.ssh/known_hosts file, and you won't be asked to connect again until either the public key on your Azure VM changes or the server name is removed from ~/.ssh/known_hosts.
If the VM is using the just-in-time access policy, you need to request access before you can connect to the VM. For more information about the just-in-time policy, see Manage virtual machine access using the just in time policy.
Next steps
Java Ssh Private Key Example
For more information on working with SSH key pairs, see Detailed steps to create and manage SSH key pairs.
If you have difficulties with SSH connections to Azure VMs, see Troubleshoot SSH connections to an Azure Linux VM.
